We will do the series of challenges from CyberGym
I won’t do the first challenge, because i can’t install the raw apk on my emulator. The apk has .so file compiled for x86 system, while my Mac can have only arm emulators.
Also, building the source itself was a daunting task I decided to give up on.
So, let’s start with the second challenge, here is the apk com.cybergym.lab2.apk.
Let’s access the app after installing it using adb:
Okay, Let’s open it using jadx and read the files.
First, from AndroidManifest.xml we can see that the name of the package is com.moksh.lab2, and that there is one activity:
<activity android:name="com.moksh.lab2.MainActivity">
<intent-filter>
<action android:name="android.intent.action.MAIN"/>
<category android:name="android.intent.category.LAUNCHER"/>
</intent-filter>
</activity>
We can see in the main activity that it first checks if the application got tempered, and then do another call to some function from the weird package defpackage.ja:
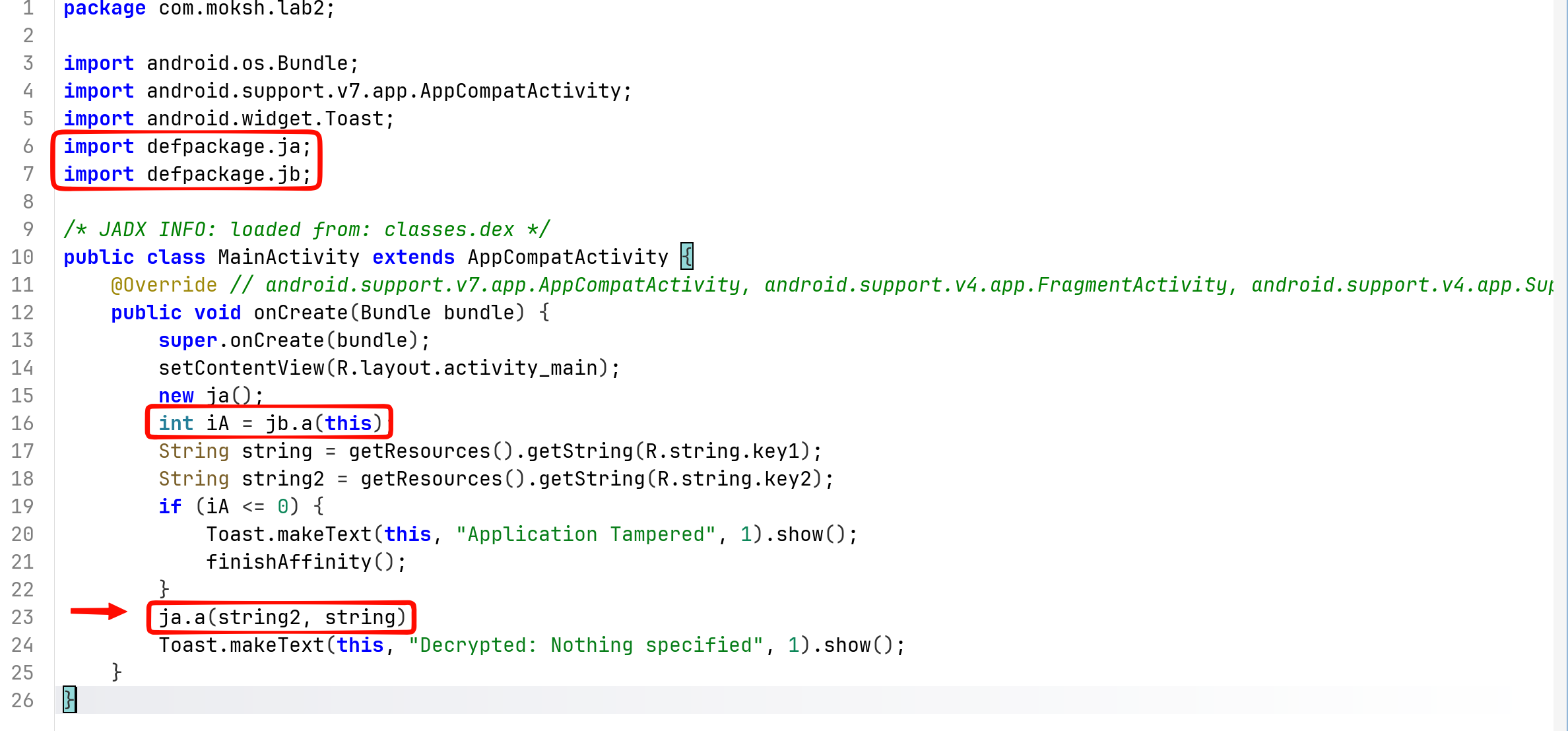
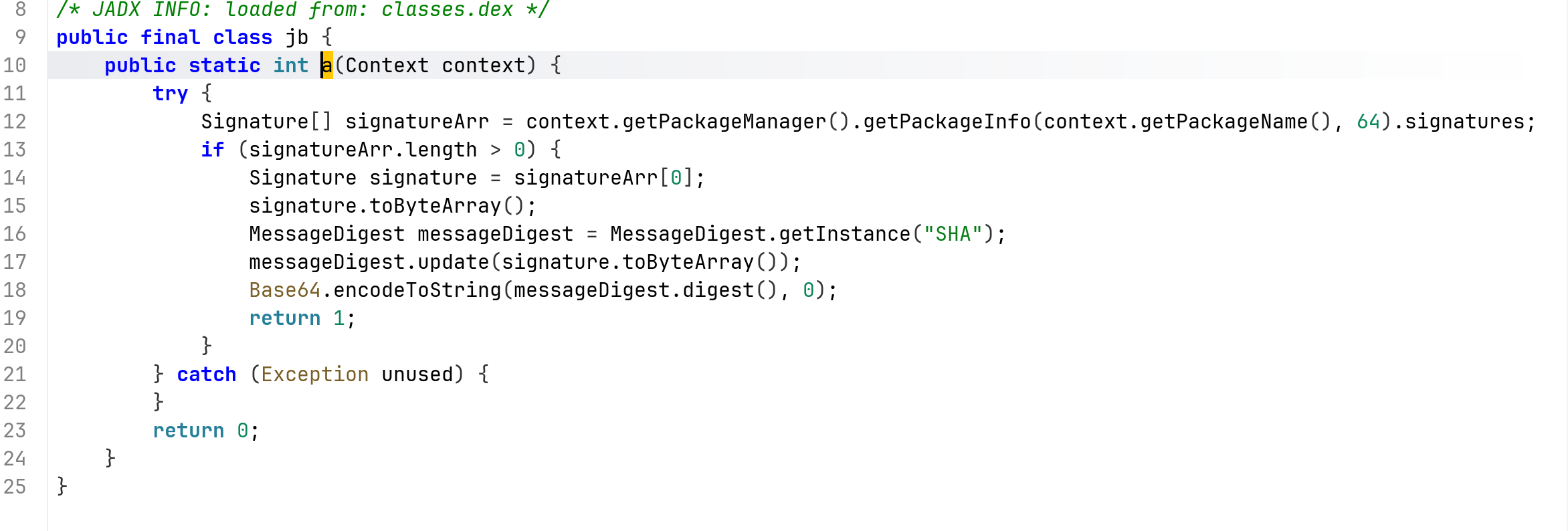
The first function actually checks for something with the application signature:
However, we don’t really want to modify the apk, and anyway we can manually sign it with our key.
The second function takes this two keys from the string.xml file:
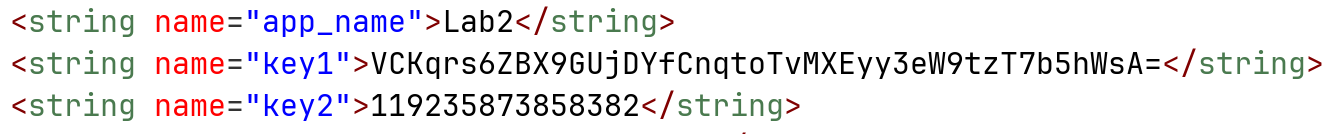
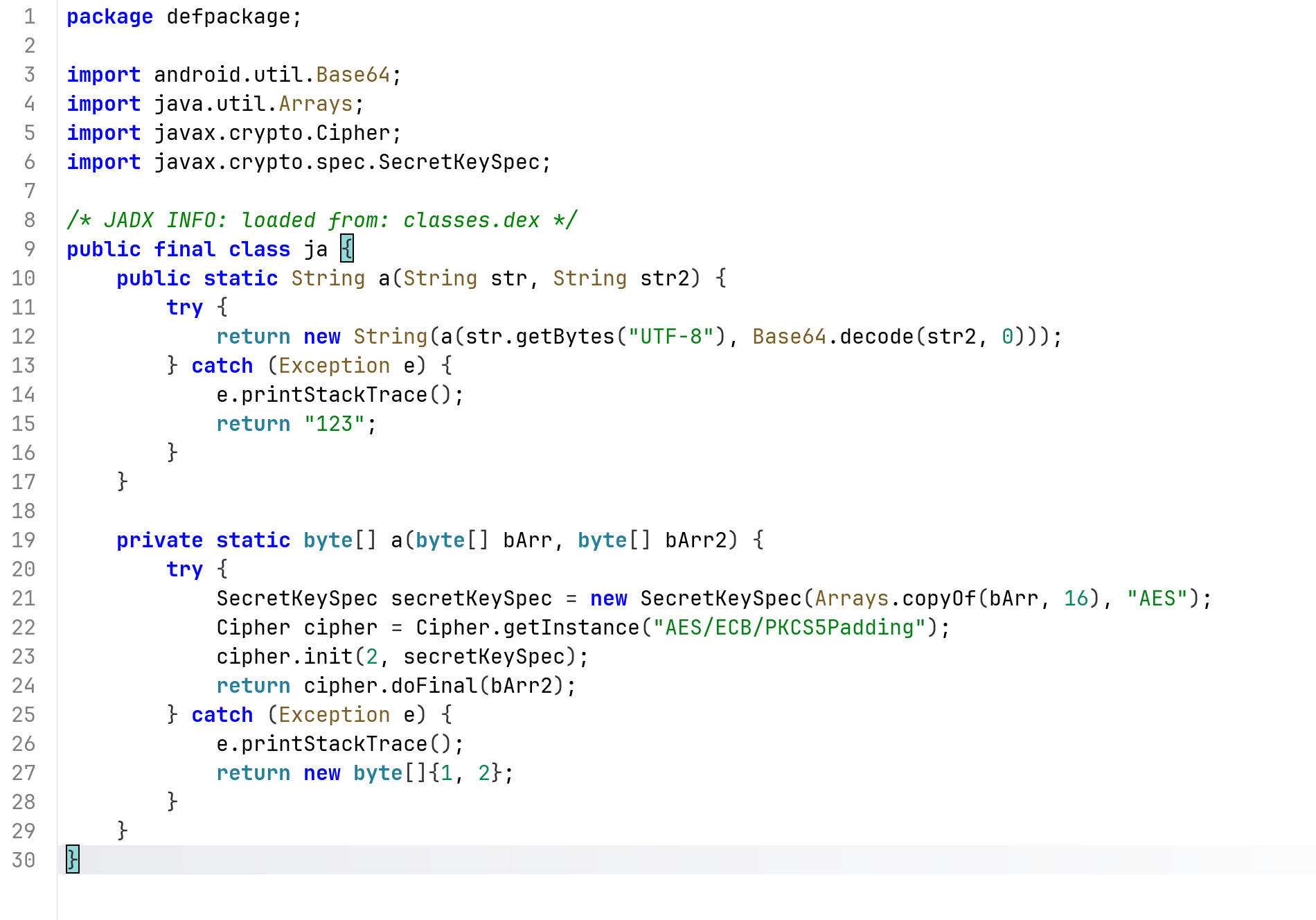
the class itself do some aes decryption, where the first key is encrypted base64 message, and the second key is the key itself for the decryption:
Let’s hook this function and print the result:
Java.perform(function() {
Java.use("ja").a.overload('java.lang.String','java.lang.String').implementation = function(str1, str2) {
const res = this.a(str1, str2);
console.log("result is: " + res);
return res;
};
}
)
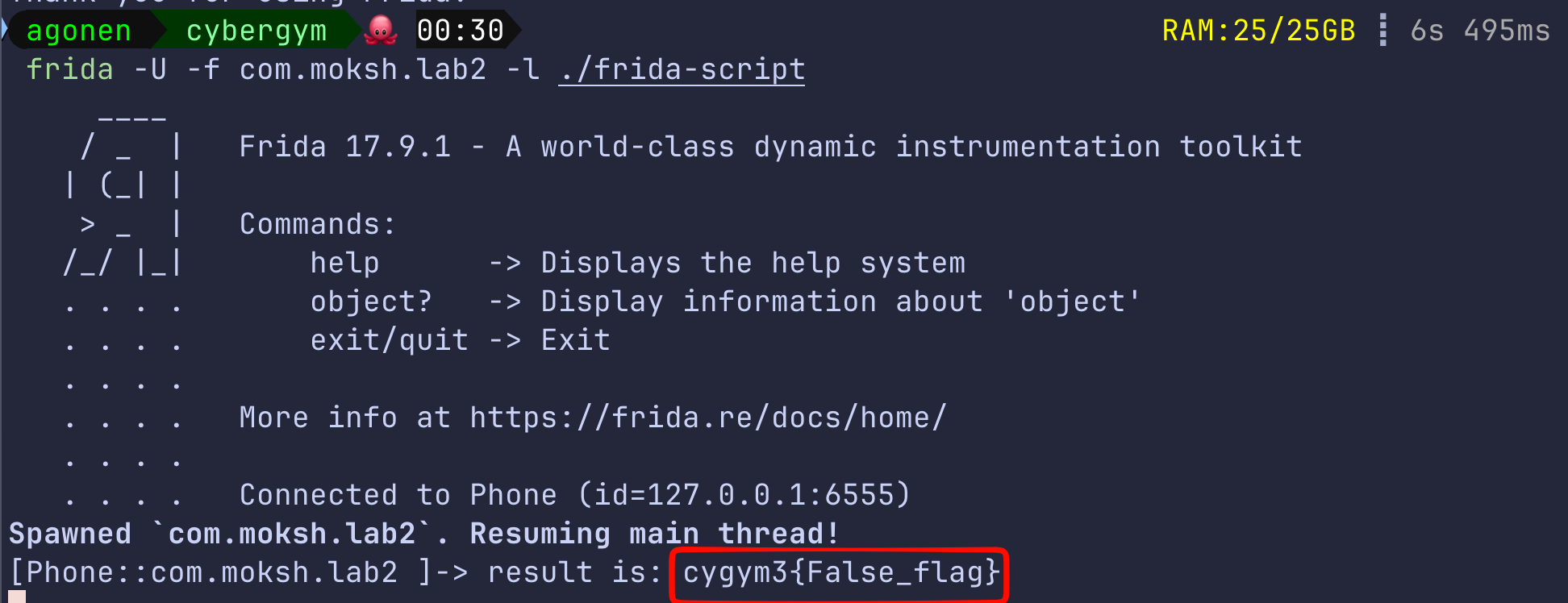
Okay, we got some false flag. Interesting.
I tried different approach, I unzipped the apk:
unzip com.cybergym.lab2.apk -d lab2/
Then, I simply searched using grep for the flag:
grep -rani "cygym3{.*}" --color *
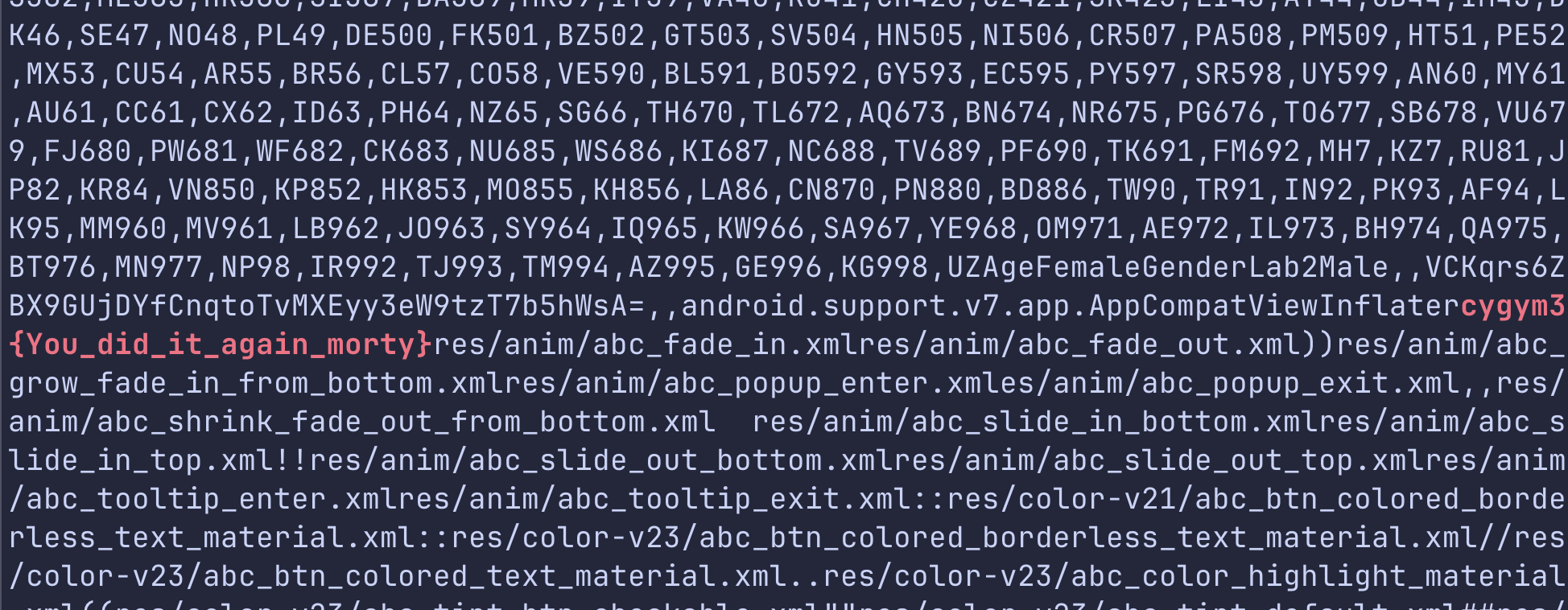
and i got this flag cygym3{You_did_it_again_morty}
lab3, first i downloaded the apk com.cybergym.lab3.apk, and installed it on the emulator using adb.
 Okay, let’s start analyze the files using jadx, first we can see main activity, and that the package name is
Okay, let’s start analyze the files using jadx, first we can see main activity, and that the package name is com.moksh.lab3:
<activity android:name="com.moksh.lab3.MainActivity">
<intent-filter>
<action android:name="android.intent.action.MAIN"/>
<category android:name="android.intent.category.LAUNCHER"/>
</intent-filter>
</activity>
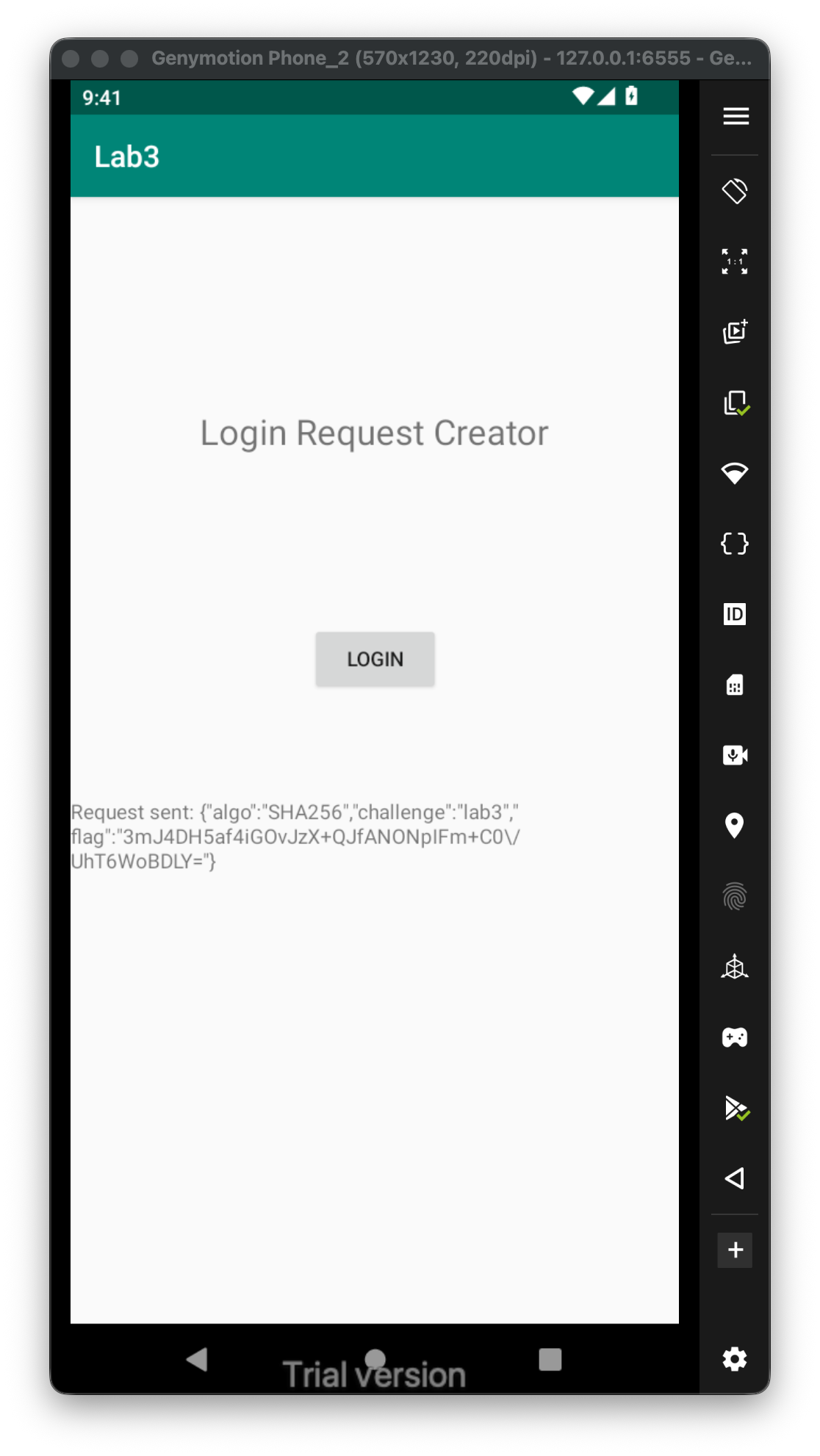
Next, we can see it first checks for tempering, same as on previous challenge. Then, it creates some json object, and send the encrypted flag.
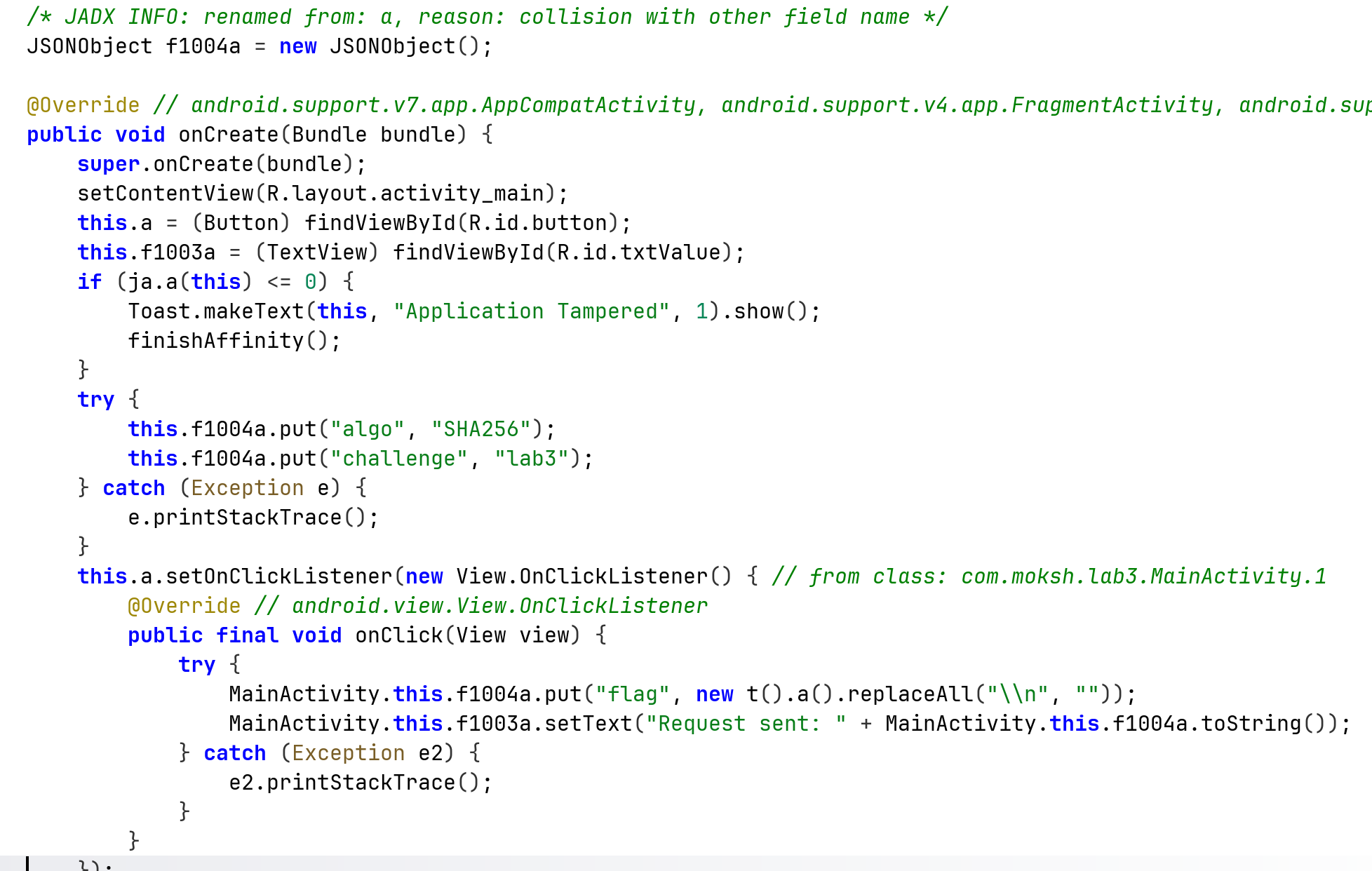
When we check the code of the class t, we can see it creates the flag, and than hash it, and send its sha256 hash:
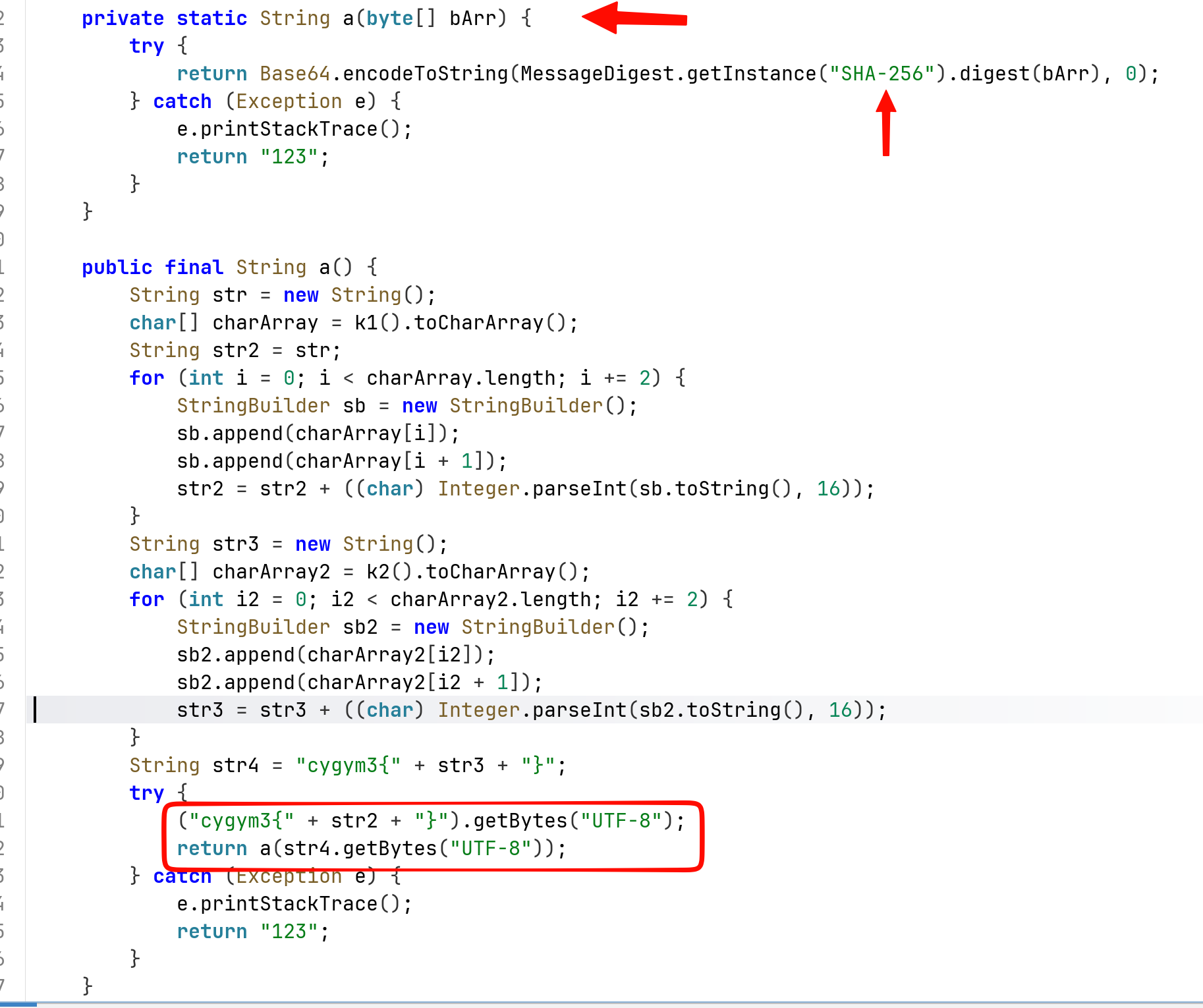
Let’s simply hook the function a with the one byte param, and grab the value moment before it get hashed. This is the code:
Java.perform(function() {
Java.use("com.moksh.lab3.t").a.overload('[B').implementation = function(bytes){
console.log("str is: " + String.fromCharCode.apply(null, bytes));
return this.a(bytes);
};
}
)
So, the flag is cygym3{Morty_solved_Frida_flag}
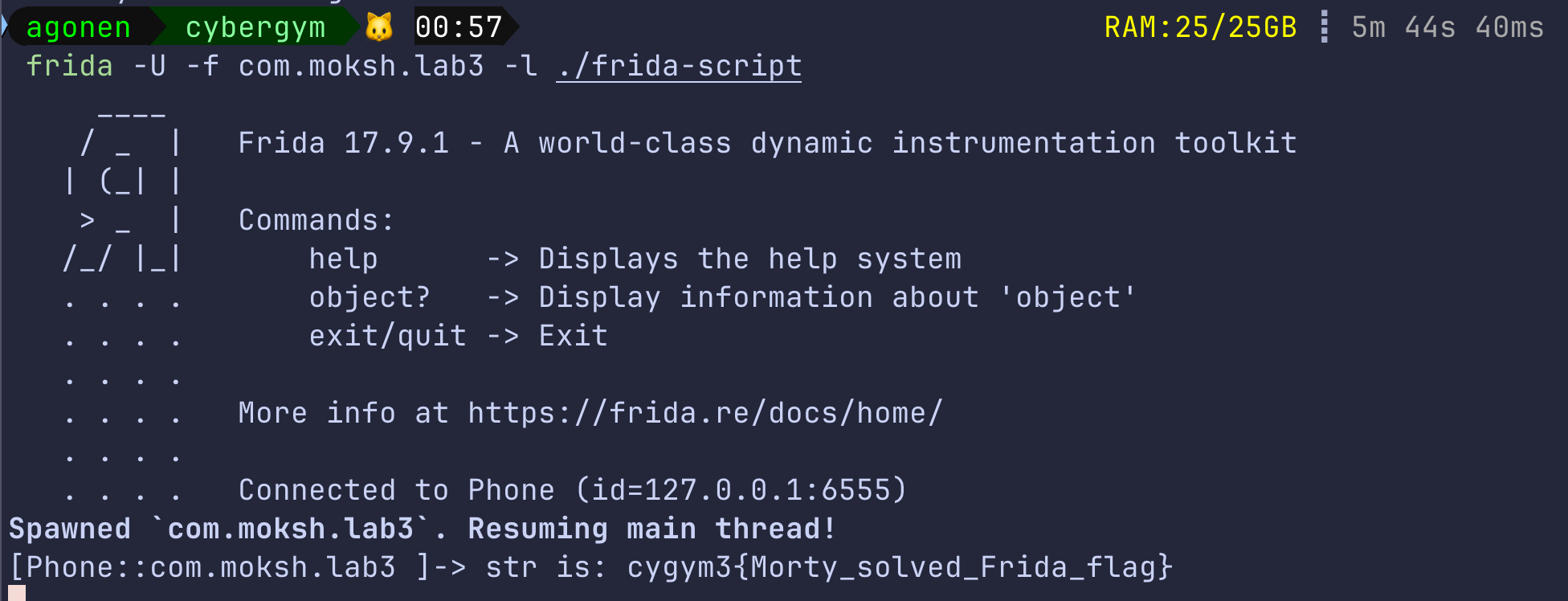
Now, we are at part4, the apk is com.cybergym.lab4.apk.
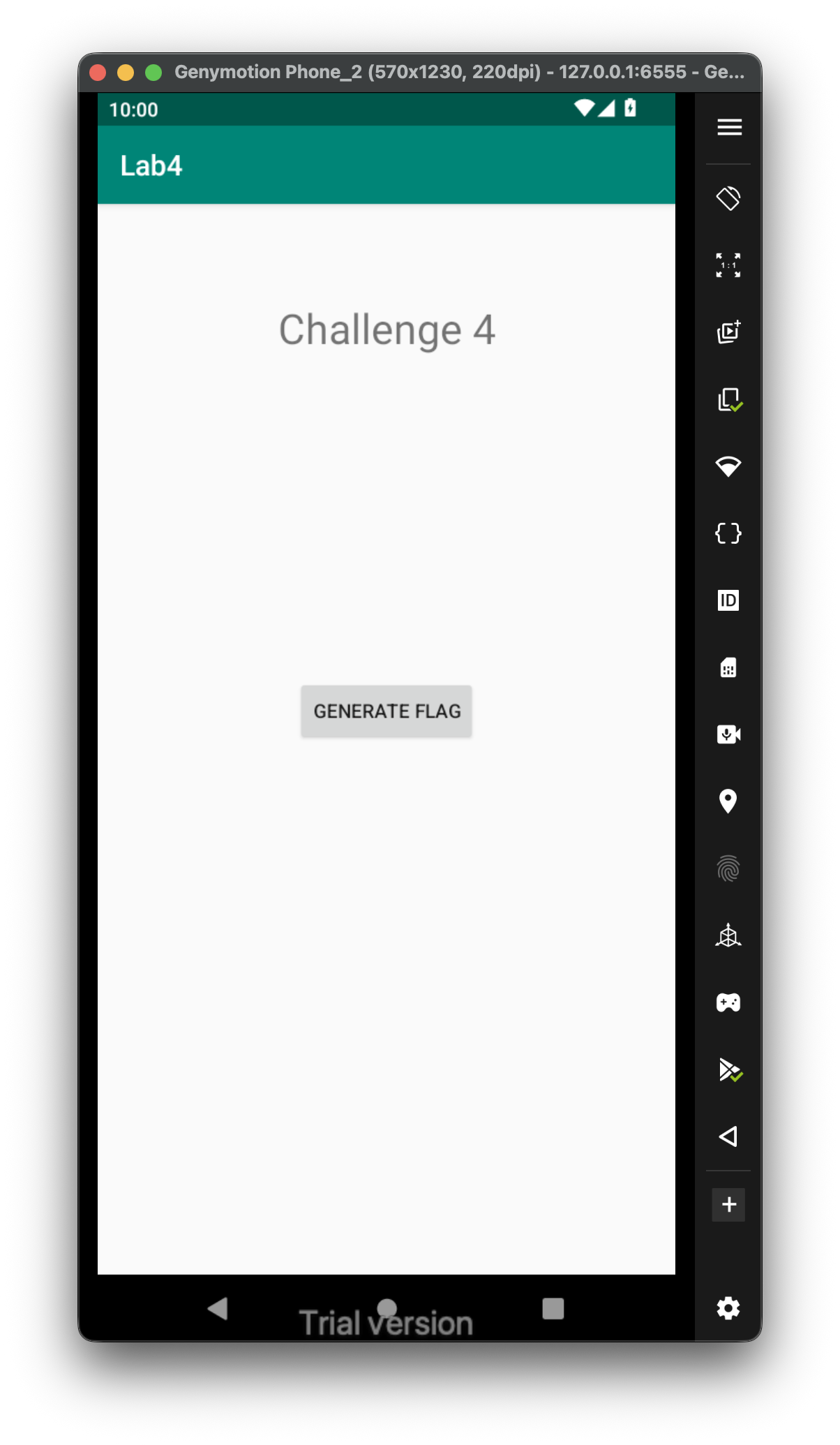 First, let’s analyze the code using jadx, again, we have one main activity and the package name is
First, let’s analyze the code using jadx, again, we have one main activity and the package name is com.moksh.lab4:
<activity android:name="com.moksh.lab4.MainActivity">
<intent-filter>
<action android:name="android.intent.action.MAIN"/>
<category android:name="android.intent.category.LAUNCHER"/>
</intent-filter>
</activity>
We can see that it has some click counter, when we reach 3 it prints the partial flag, and when we reach 10 it resets the counter.
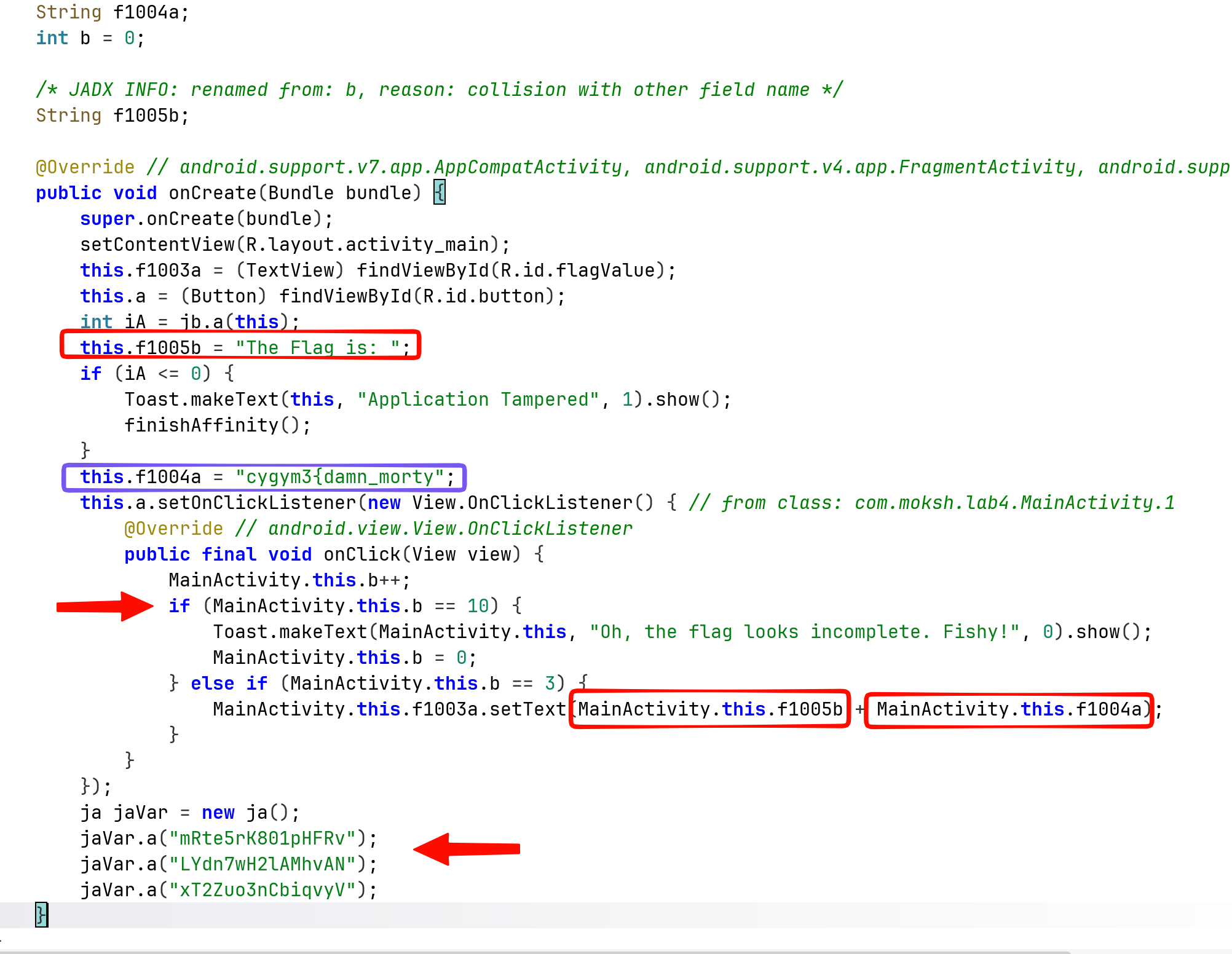
Also, there is something at the bottom, looks like some encoded or encrypted strings, let’s dive into this class.
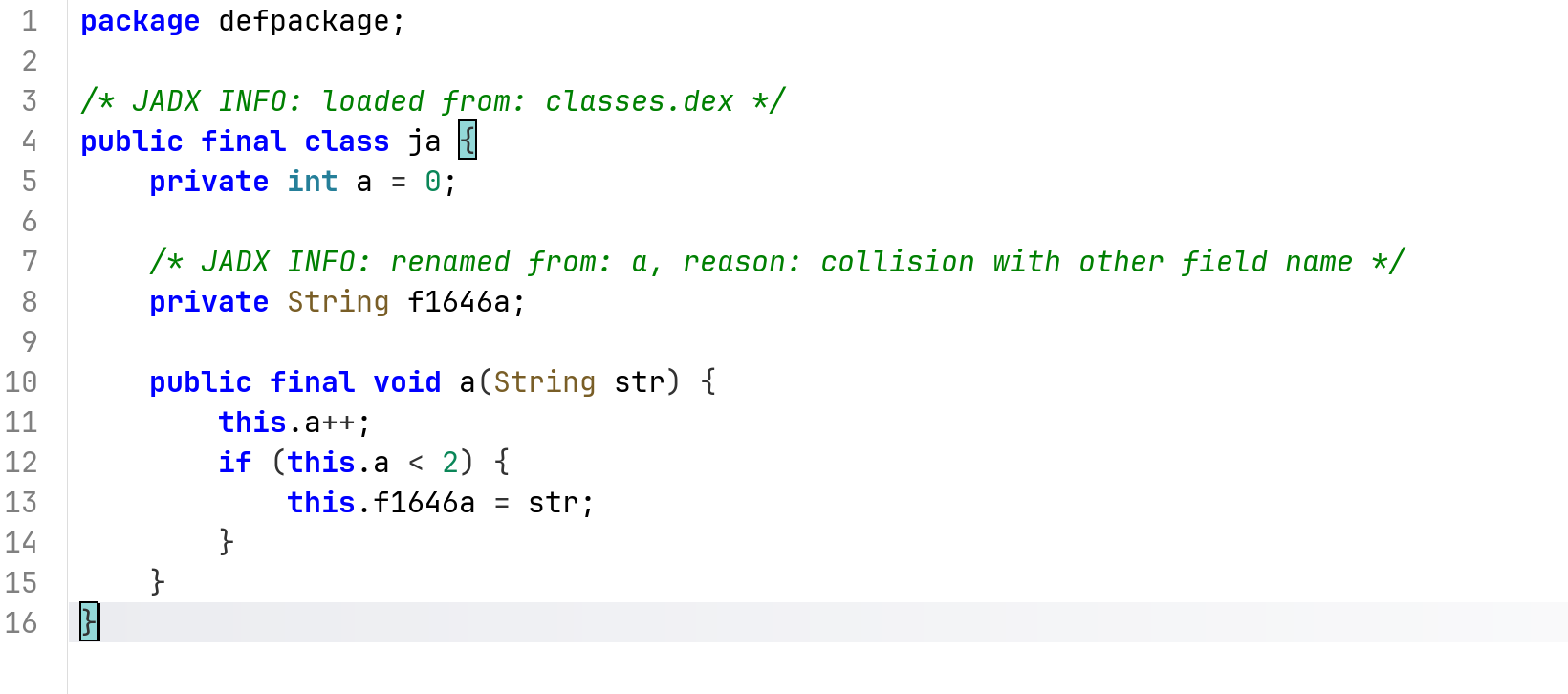
The code here looks very simple, it saves the two first strings it gets, and that’s all.
I looked at the strings.xml and found that it has firebase url:
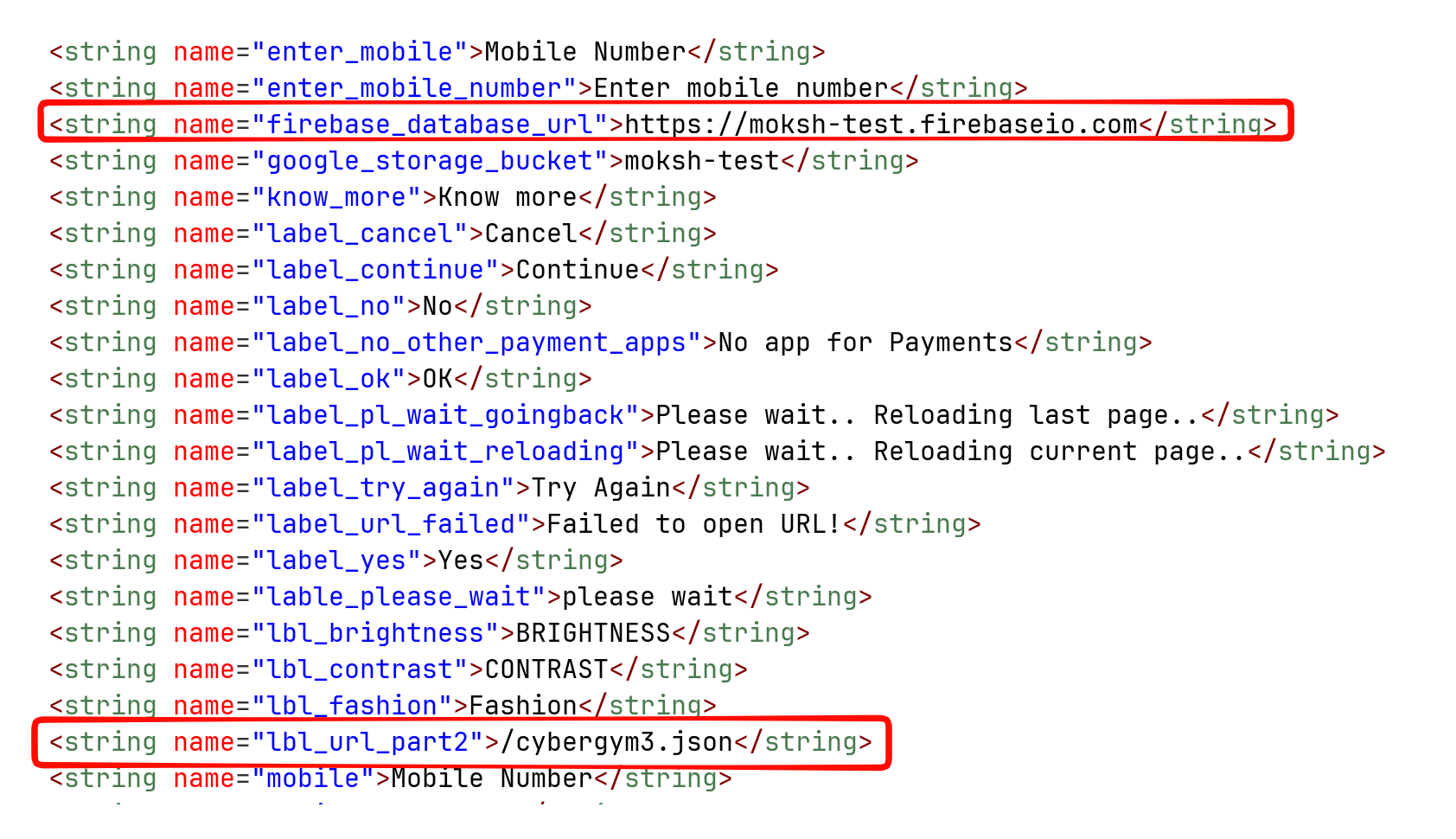
We got two interesting values, first the url https://moksh-test.firebaseio.com, and second, the lbl_url_part2, which is /cybergym3.json.
Let’s try to access the firebase database, on this path:
https://moksh-test.firebaseio.com/cybergym3.json
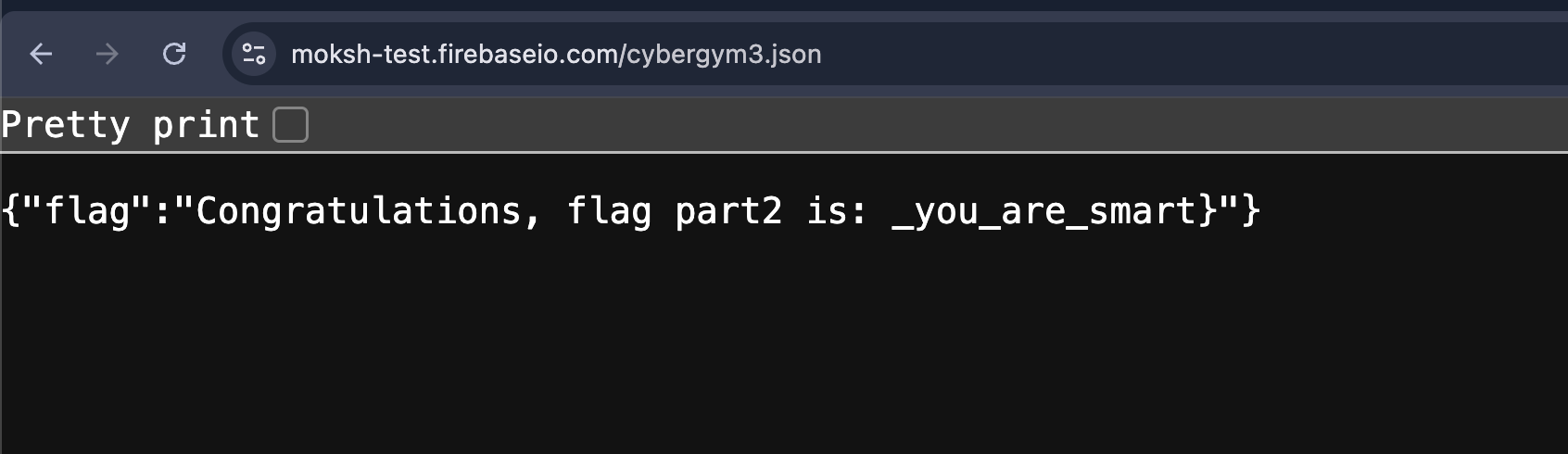
So, we got the second part of the flag :)
remember, the first part was cygym3{damn_morty, so the full flag will be:
cygym3{damn_morty_you_are_smart